A malicious Bitwarden CLI package ran during npm install, before anyone had a chance to inspect it. That is exactly the kind of supply chain story the agentic era keeps repeating.
April 23, 2026 · Supply chain / agent runtime
Bitwarden did not suffer a broad compromise of its vaults or production systems. What happened was narrower and more instructive: a malicious @bitwarden/[email protected] package was briefly distributed through the npm delivery path for the CLI between 5:57 PM and 7:30 PM ET on April 22, 2026. The affected window was short, and the blast radius was limited to that npm CLI path.
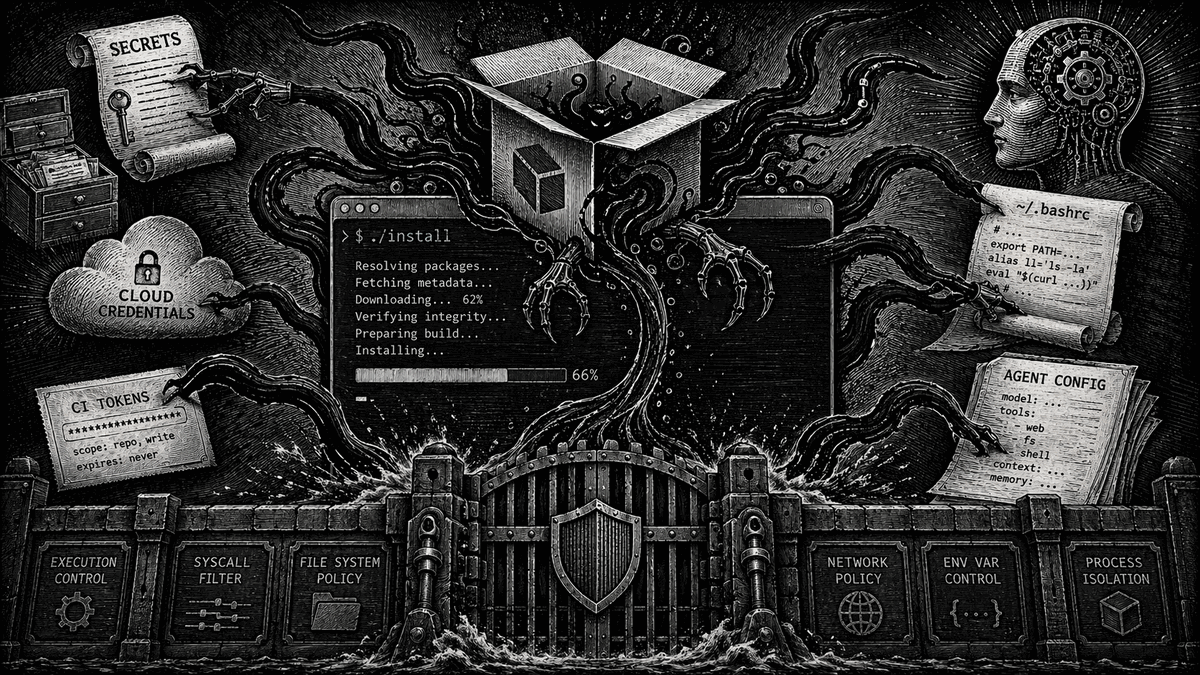
The important part is not just that a trusted package was poisoned.
It is where the payload ran.
Researchers found that the malicious package rewired the preinstall path and the bw entrypoint to a custom loader that downloaded Bun and launched a second-stage payload. That means npm install @bitwarden/cli was enough.
The payload ran during preinstall, before npm had even finished handing control back to the user.
Post-install inspection is too late by construction.
That matters even more in the agentic age. A human might or might not install a bad version during a short exposure window. A CI fleet running npm install on every push, a bot auto-resolving latest, or an agent spinning up fresh per-task sandboxes can hit that window without a human in the loop.
Agent workflows do not stop at the command boundary. They run installs, setup steps, tests, and child processes continuously.
This was not just credential theft
The payload went after GitHub and npm tokens, SSH keys, shell history, .env files, cloud credentials, CI secrets, and AI tooling configuration. It also used memory scraping in CI, not just file scraping, which is an important reminder that "protect the obvious files" is not enough on its own.
But the detail that makes this story specifically about the agentic era is what it did to the shell.
Security Boulevard's syndicated Mend analysis says the malware appended a roughly 3.5 KB "Butlerian Jihad" manifesto into shell profile files using a quoted heredoc block that does not execute in the shell but still remains in the file.
That matters because coding assistants often read files like .bashrc and .zshrc to understand the environment.
So the payload lands in the assistant's context window even when it is inert to the shell itself.
That is not just persistence.
It is an attempt to poison the next agent.
The shell is no longer just a persistence target. It is part of the model's working context.
AI tooling is now a first-class target
The malware targeted AI tooling configuration files such as ~/.claude.json, ~/.claude/mcp.json, and ~/.kiro/settings/mcp.json.
Modern developer environments now include agent configuration as a first-class target.
This is what the next supply chain incident looks like: not just credential theft from disk, but theft from CI, abuse of developer tokens, and direct targeting of the files that shape how agents behave.
What execution-layer security actually does here
The point of AgentSH is not to replace detection.
It is to make detection operational at the moment of execution.
AgentSH secure-sandbox added package install security checks that intercept install commands like npm, pip, and yarn and check packages against security providers including Socket before allowing the install. It also added packageRules so policy can block malware, require approval, or flag risky packages.
For an incident like this, that is the difference between "we learned about it quickly" and "the install never happened."
That is especially important here because the compromise point was preinstall. If you do not stop the package before install-time scripts run, you are already behind.
AgentSH also governs what happens inside the command, not just the command itself. Its runtime policy model supports allow, deny, approve, soft_delete, and redirect, with visibility into file I/O, network connections, process activity, PTY activity, and LLM API traffic.
That matters here because the malicious loader still had to do real work after npm install started: download runtime components, read secrets, inspect AI config, touch shell profiles, and open outbound network connections.
Runtime controls let you govern those side effects directly.
And when autonomy should stop, approvals need to exist at the execution boundary, not the planning boundary. Agents do not have a built-in half-second pause when something looks off. Deterministic approvals put that pause back where it matters.
The lesson
The most important sentence in this incident is simple:
The payload ran before npm finished installing.
That is why this matters so much for autonomous systems. A short exposure window is good. But short windows stop being reassuring when agents and CI workflows can still hit them automatically, and when the malware is not content just to steal credentials from disk.
In this case it also targeted AI tooling config and, according to Security Boulevard's syndicated Mend analysis, tried to poison the context window of the next assistant that read the shell profile.
Socket for fast ecosystem detection. AgentSH for deterministic enforcement at execution time.
Detection without runtime control means you can learn about the compromise quickly and still lose.
Sources
- Socket: Bitwarden CLI Compromised in Ongoing Checkmarx Supply Chain Campaign
- Bitwarden statement on the Checkmarx supply chain incident
- JFrog: Bitwarden CLI hijack analysis
- Security Boulevard / Mend: The Butlerian Jihad compromised Bitwarden CLI
- AgentSH secure-sandbox releases
- AgentSH repository
Built by Canyon Road
We build Beacon and AgentSH to give security teams runtime control over AI tools and agents, whether supervised on endpoints or running unsupervised at scale. Policy enforced at the point of execution, not the prompt.
Contact Us →